Secure VPN Access to AWS Resources
Infrastructure-as-code implementation of multi-environment VPN architecture for secure remote access to cloud resources
Project Background
This project was developed for Vanderbilt University's Computer Networks course to demonstrate cloud networking fundamentals, network security controls, and infrastructure-as-code implementation. Using Terraform and AWS, I built a VPN infrastructure that showcases VPC design, subnet configuration, security groups, routing tables, and encrypted tunneling with OpenVPN.
The implementation spans three isolated environments (development, QA, and production), each demonstrating environment isolation, network segmentation, and declarative infrastructure management. The focus is on applying networking principles correctly and using infrastructure-as-code to build reproducible, version-controlled cloud infrastructure.
Project Objectives
Build a production-ready VPN solution demonstrating:
Infrastructure Automation:
- All cloud resources declared as code, enabling version control and repeatable deployments across environments without touching the AWS console.
Network Security:
- Secure remote access using OpenVPN, providing encrypted tunnels that let authorized users access private cloud resources as if they were on the internal network.
Environment Isolation:
- Identical architecture across dev, QA, and production with isolated networks, demonstrating proper separation of concerns and safe testing workflows.
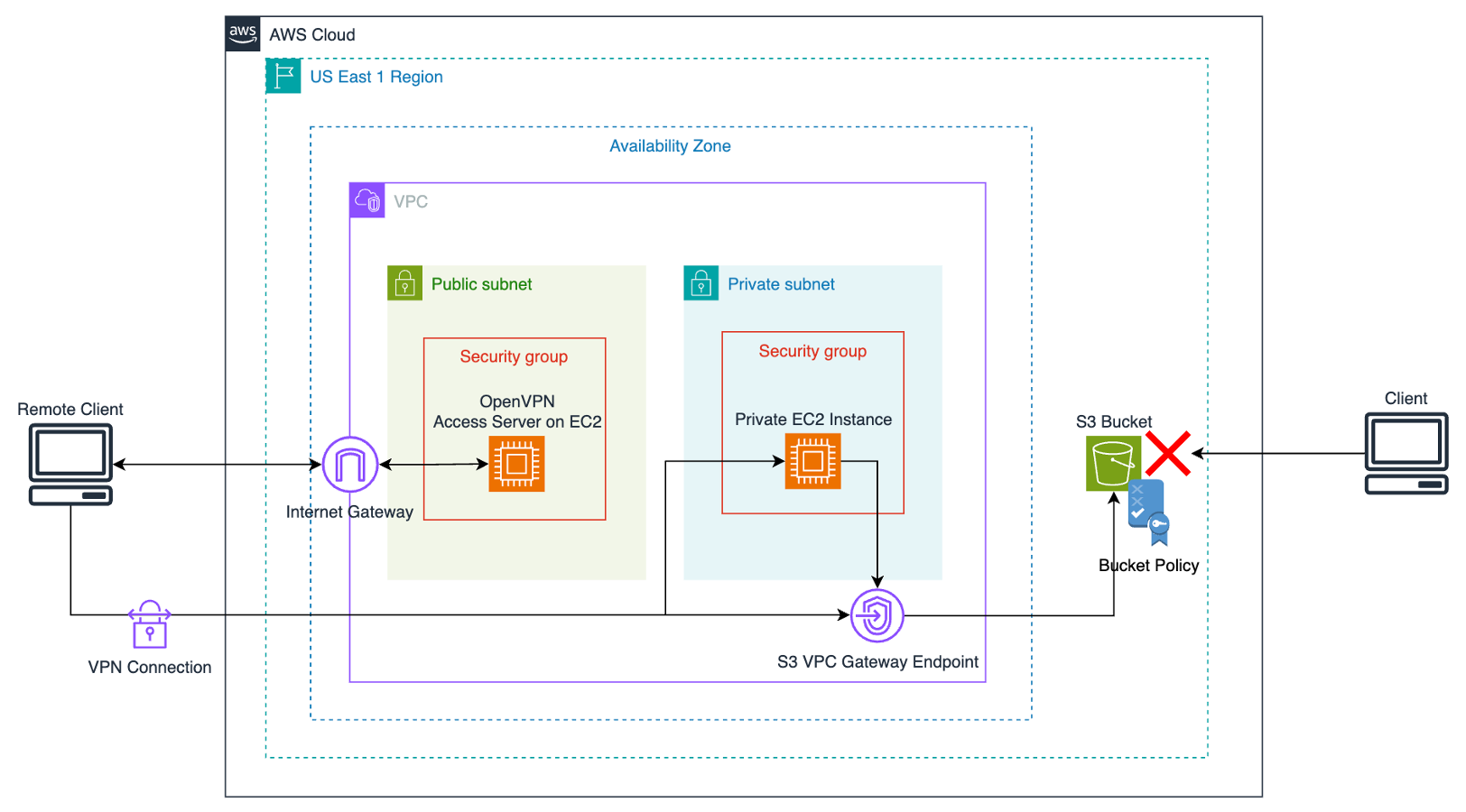
Architecture
Network Module
Establishes the AWS networking foundation: VPC with public and private subnets across availability zones, routing tables controlling traffic flow, internet gateways for public connectivity, and NAT gateways enabling private resources to reach outbound while staying unreachable from the internet. Security groups define firewall rules controlling protocol and port access to VPN and application resources.
Servers Module
Provisions EC2 instances hosting OpenVPN Access Server. Handles instance sizing, security group association, and Elastic IP allocation so the VPN endpoint maintains a consistent public address. Uses the OpenVPN Access Server marketplace AMI, avoiding manual installation and baseline configuration.
Storage Module
Creates S3 buckets hosting static web content for connectivity validation. Bucket policies allow private access through the VPN tunnel while blocking public internet access, demonstrating a common pattern for securing cloud applications behind VPN infrastructure.
Environment Configuration
Three parallel environments use Terraform workspaces and input variables, allowing identical module code to provision isolated DEV, QA, and PROD deployments. Environment-specific variables control CIDR blocks, instance sizing, and resource naming. Changes validate in development, test in QA, then apply to production with confidence.
Implementation
Repository Structure
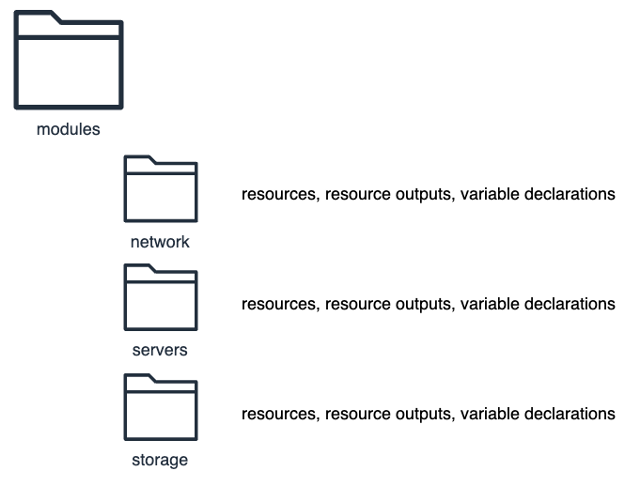
The Terraform project uses a modular structure separating reusable infrastructure definitions from environment-specific configurations:
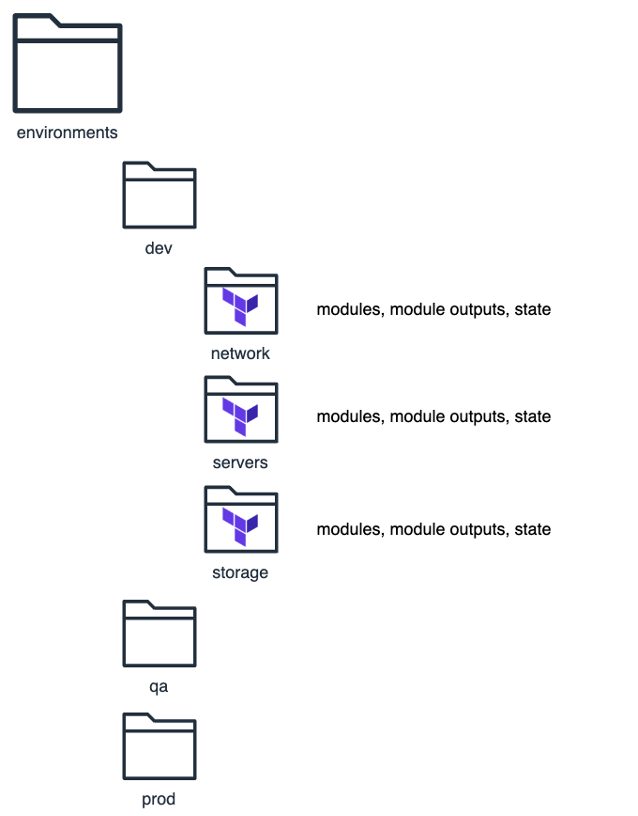
Each module directory contains resource declarations, output definitions, and variable declarations that define the infrastructure components. Environment directories instantiate these modules with environment-specific variables, maintaining separate state files for each module within each environment. This structure enables independent module deployment and updates while maintaining environment isolation.
VPN Layer
OpenVPN Access Server provides the VPN implementation. Administrators provision users through a web portal and distribute secure token URLs. Users redeem tokens to download connection profiles containing certificates, keys, and server details, then use OpenVPN Connect to establish encrypted tunnels.
Connected clients route traffic through the VPN server, which bridges them to the private VPC network. This grants access to resources on private subnets with no direct internet connectivity, including the S3-hosted test application.
The server uses TLS encryption for control channels and AES for data channels, handling key exchange, perfect forward secrecy, and certificate-based authentication automatically.
Infrastructure Layer
Terraform HCL files declare all AWS resources as code. The environments/ directory contains variable definitions for each environment, while modules/ contains reusable resource declarations. Key patterns:
- Module composition:
- Main configurations reference reusable modules with environment-specific inputs
- Variable abstraction:
- Environment differences handled through variables, not code duplication
- Output exposure:
- Modules export values for cross-module dependencies
- State management:
- Terraform tracks deployed resources, enabling safe modifications
Application Layer
The 03 - application/ directory contains a test webpage deployed to S3. Access policies restrict connectivity to VPN-connected clients. Successfully loading this page validates the VPN tunnel and private network routing.
Outcomes
This project demonstrates practical infrastructure-as-code and network security in cloud environments:
- Modular infrastructure design with reusable Terraform components
- Security best practices: network isolation, least privilege access, encrypted communication
- Multi-environment workflows enabling safe testing before production deployment
- Operational foundation for secure remote access with automated provisioning enabling rapid deployment and modification
The result is production-ready infrastructure providing secure remote access to cloud resources, with declarative configuration supporting version control, peer review, and repeatable deployments.